Understanding WASA Audits: ABDM Compliance Simplified.
Web applications play a pivotal role in business operations and customer interactions. However, this increased reliance on web applications also makes...
To find a web application's vulnerabilities, web app security testing is an essential procedure. With the increasing adaptation of web technologies across several areas, web applications have become a very viable attack surface if left with an untailored security outlook. Hence, assessments like web application security help the developers remediate vulnerabilities that are found during the process thereby and enhance the overall security of the web application.
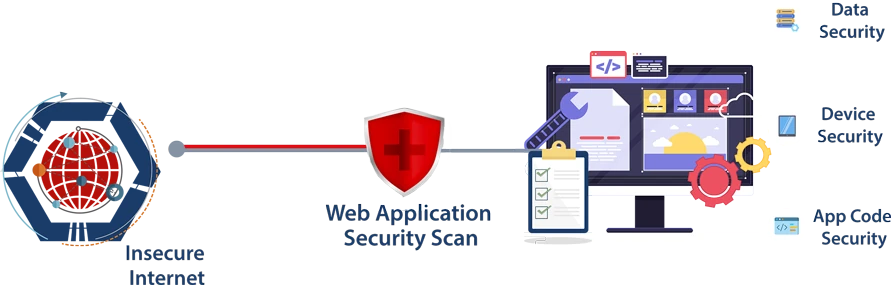
Web application security testing as per the OWASP Top 10 list, helps to identify many unattended issues related to programming, file access and configuration etc which may turn out to be vulnerabilities, causing a potential impact on the organization.
Regular assessments as such help safeguard the application from any unauthorized access which can cause an impact on the organization both in reputation and resources.