System and Organization Controls (SOC) are important assurance reporting frameworks in the context of SOC Compliance. These frameworks are designed to help service organizations establish confidence and trust between stakeholders, entities, and service providers. The controls are standards designed to assist service organizations in imparting services to their clients & customers and helping them meet the internal and external stakeholders' demand for trust, transparency, contractual obligations and marketplace concerns.
The SOC reports aid in providing reasonable assurance to companies that their service providers have demonstrated capability of controls on security, availability, confidentiality, processing integrity and privacy ensuring that the organizations are operating in an ethical and compliant manner.
SOC Assessment And Audit Reports Are Classified Depending On Their Usage And Service Controls.
SOC 1 : Pertaining to ICFR, this reporting covers the controls of service organization over its end user’s financial reporting. This is classified under two categories Type 1 reporting & Type 2 reporting.
SOC 2 : Concerned for Service Organization’s Trust Services Criteria (TSC). It defines controls necessary at a service organization that are relevant to Security, Availability, Processing Integrity, Confidentiality and Privacy. This is classified under two categories Type 1 reporting & Type 2 reporting.
SOC 3 : Done in line with SOC 2 reporting, SOC 3 reporting is meant for general use or for customers who need assurances regarding the necessary controls maintained and managed by the organization.
SOC Cybersecurity : AICPA has issued a Cybersecurity Risk Management Reporting Framework, through which a CPA reports on an organization's enterprise-wide cybersecurity risk management program.
Why Is SOC Compliance Important?
The American Institute of Certified Public Accountants (AICPA) developed a set of voluntary standards referred to as Service Organization Controls. These standards offer organisations a framework for dealing with client data and demonstrating their commitment to data safety. A SOC/SSAE Assessment report is obtained via a planned and detailed audit process that examines the service organisation's controls, confirms their efficacy, and generates a complete report documenting the results. A Certified Public Accountant (CPA) company with experience doing SOC audits works in unison with the business requesting the report to complete this process.
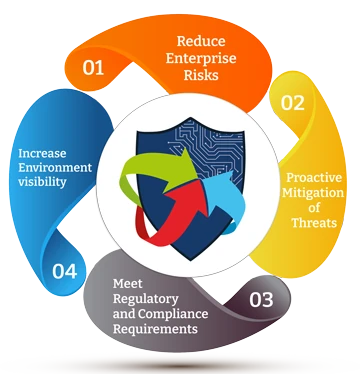
SOC compliance is becoming increasingly important for several reasons:
- Meeting Regulatory Requirements: Data protection policies are required by laws in several fields, including banking and healthcare. Organisations can fulfil these criteria and perhaps avoid penalties with the aid of SOC compliance.
- Building Customer Trust: The safety and confidentiality of their personal information is a growing issue for customers. Organisations may show their customers that they have the best data protection practices in place by becoming SOC-compliant.
- Combating Cyber Threats: Organisations must have strong security measures in place due to the increasing frequency and complexity of cyber-attacks. A company may rest easy knowing it has taken enough precautions to safeguard itself from these risks if it is SOC-compliant.
Who Needs SOC Compliance?
SOC compliance audits apply to all companies irrespective of their size or industry. A SOC compliance audit assesses a business's ability to effectively mitigate the risks associated with managing sensitive customer data via electronic communication or ICT (Information and Communication Technology). A SOC report is useful for every company that deals with customer data. SOC compliance is very important in a number of businesses, including:
- Cloud Service Providers
- SaaS (Software as a Service) Providers
- IT Outsourcing Companies
- Healthcare Organizations
What Are SOC 1, SOC 2, SOC 3 And SOC Cybersecurity?
-
SOC 1
SOC 1 reports assess the effectiveness of a service organisation's internal controls over financial reporting. This report is used by service providers to demonstrate compliance with FINRA, SEC, and SOX regulations. SOC 1 reports are prepared by external auditors for use by both government agencies and service organisation customers.
When is SOC 1 required?
Businesses often need a SOC 1 compliance report from the service providers they engage in order to guarantee accurate financial reporting. Businesses should confirm that the service provider has put in place sufficient service controls in order to get trustworthy financial reporting.
-
SOC 2
A service provider's information systems and controls for security, availability, processing correctness, confidentiality, and privacy are examined in relation to a set of reporting and tracking requirements in order to ensure SOC2 compliance. SOC 2 is a mandate for businesses such as banks, SaaS providers, and healthcare providers that handle or keep private consumer data. The AICPA developed the SOC2 standard to ensure that service providers fulfil legal requirements and protect customer data. It is assessed based on the five Trust Services Criteria prescribed by AICPA.
When is SOC 2 required?
SOC 2 is essential for businesses that deal with confidential information and want to show their consumers and clients that they have adequate security measures in place for storing and processing data.
-
SOC 3
A SOC 3 report tells the public about the availability, trustworthiness, and privacy of an organisation's internal security controls. While both SOC 2 and SOC 3 concentrate on security, the latter is intended for a broader audience and is thus less rigorous.
When is SOC 3 required?
Businesses utilise SOC 3 as a promotional tool, handing out copies to potential clients so they can get an understanding of the company's security procedures and level of compliance with industry standards.
-
SOC for Cybersecurity
The SOC for Cybersecurity is a separate SOC framework from the more common SOC 1, SOC 2, and SOC 3 certification standards. It addresses cybersecurity issues for all types of enterprises, from service providers to manufacturers. In contrast to SOC 2 attestations, the goal of this report is to detail the specifics of an organisation's cybersecurity initiatives and how they are being implemented. These reports are aimed at the general public rather than experts.
What Makes QRC the Best Choice for SOC Compliance?
- Qualified CPA Firm: QRC is a Delaware-registered CPA firm with a team of qualified auditors. Our team comprises the most experienced and qualified individuals and follows strict AICPA guidelines to ensure the accuracy and integrity of our audits.
- Experienced CPA/CA Professionals along: Our SOC compliance specialists are qualified CPAs and CAs with the expertise and accreditation to do thorough audits. This guarantees our customers get the best compliance guidance and expertise.
- Multiple Credentials: QRC is a PCI QSA Assessor for PCI DSS, PCI 3DS, PCI SSF, company along with an ISO Certification, Accredited Certification body for ISO/IEC 27001 & ISO/IEC 27701, CERT-IN empanelled, qualified to provide even other assessments like SOC/SSAE Certifications, GDPR, HIPAA along with other security testing services, showcasing our commitment to information security, privacy, and quality.
- Aligning Compliance with Local Regulatory Requirements: With rigorous audits and evaluations, our skilled personnel evaluate your organisation's controls in order to certify their compliance as per local regulatory requirements of their state.