Cyber security is all about defense and Squid Game.
An organization’s network system, attackers with risks awaiting to enter the network and security....
Mobile application security testing is performed to identify the vulnerabilities in a mobile application. In recent years, a surge in the usage of mobile technology has been observed and is only considered to be growing. With these scales of adaptation, we have seen rising incidents of mobile security. Cyber criminals are developing more precise and accurate programs that make use of the very viable mobile attack surface if left with an untailored security outlook.
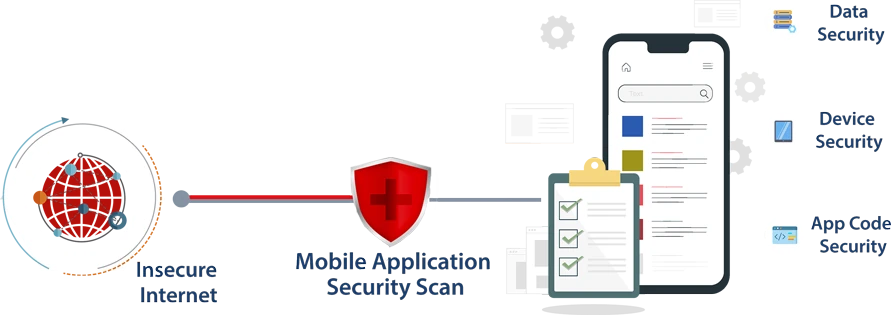
Hence, assessments like mobile application security help the developers remediate vulnerabilities on both Android and iOS platforms, found during the process thereby and enhance the overall security of the web application.
Mobile application security performed as per OWASP Mobile TOP 10, helps to identify many unattended issues related to the client-side, server-side, file system, mobile hardware and network etc which may turn out to be vulnerabilities, causing a potential impact on the organization. Regular assessments as such help safeguard the application from any unauthorized access which can cause an impact on the organization both in reputation and resources.